 Streamline Wi-fi Certificate Access In 2025
Streamline Wi-fi Certificate Access In 2025To boost your X.509 authentication, using Keytalk is a smart solution. It simplifies certificate management, automating issuance, renewal, and revocation processes, which enhances your security posture. You’ll benefit from seamless integration with existing systems and a user-friendly interface https://newscerr.com/certificate-lifecycle-management/ that reduces human error. Plus, robust encryption protects your data during transmission. With Keytalk, you can streamline operations and strengthen your security measures effortlessly. Discover how you can further enhance your authentication strategy with the right tools.
Key Takeaways
- Keytalk automates the issuance, renewal, and revocation of X.509 certificates, enhancing efficiency and reducing manual errors. Centralized visibility provided by Keytalk identifies vulnerabilities and potential threats, strengthening overall security. Robust encryption protocols in Keytalk protect data during transmission, safeguarding against eavesdropping and man-in-the-middle attacks. Seamless integration with existing systems ensures strong authentication practices without overhauling infrastructure. Automated alerts notify users of impending certificate expirations, facilitating timely renewals and maintaining secure communications.
Understanding X.509 Authentication
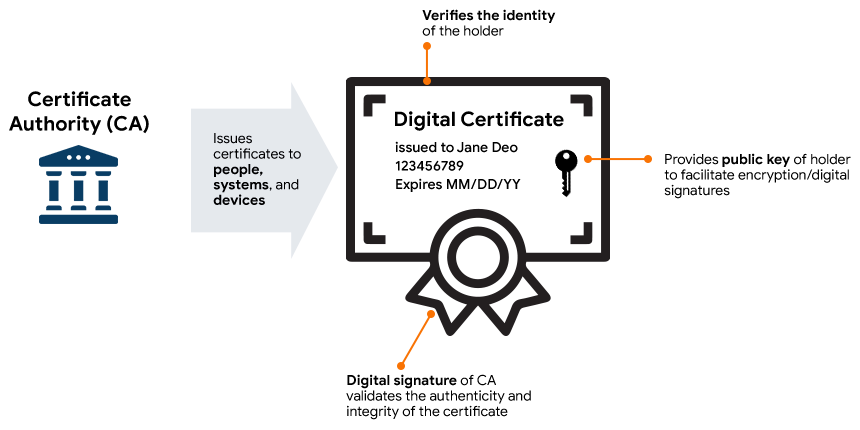
When you plunge into X.509 authentication, you’ll find it’s a critical part of secure communications on the internet. It’s a standard that defines the format for public key certificates, which help establish trust between parties.
Each certificate contains the public key, along with information about the certificate holder and the authority that issued it. By using these certificates, you can verify identities and encrypt data, ensuring that only intended recipients can access it.
Understanding the structure of these certificates is essential for implementing secure connections, as they provide the necessary framework for authentication.
With X.509, you’re not just protecting information; you’re also building a foundation of trust, which is crucial in today’s digital landscape.
The Importance of Digital Certificates
Digital certificates play an essential role in establishing trust within networks by verifying identities.
They enable secure communication protocols, ensuring that your data remains private and protected.
Without them, authentication and identity verification would become considerably more challenging, exposing you to potential risks.
Trust Establishment in Networks
Trust in networks hinges on the effective use of digital certificates, which authenticate the identities of individuals and devices.
These certificates act as digital passports, ensuring that only authorized users gain access to sensitive information. When you implement digital certificates, you foster a secure environment where data integrity and confidentiality are prioritized.
This trust establishment is essential, especially in today's interconnected world, where cyber threats are rampant. Without these certificates, it’s easy for malicious actors to impersonate legitimate entities, jeopardizing network security.
Secure Communication Protocols
To maintain secure communication in networks, implementing robust protocols is essential, and digital certificates play a vital role in this process.
These certificates verify the identity of entities, ensuring that data is exchanged only between trusted parties. When you use secure communication protocols like TLS or SSL, digital certificates encrypt the information being transmitted, protecting it from eavesdroppers and malicious actors.
This encryption not only safeguards sensitive data but also helps establish trust between clients and servers. By validating the authenticity of each party, digital certificates prevent man-in-the-middle attacks and bolster overall network security.
Embracing these protocols with digital certificates is fundamental for fostering a safe online environment and ensuring the integrity of your communications.
Authentication and Identity Verification
While many people overlook the significance of authentication and identity verification, they're essential for maintaining security in digital communications.
Digital certificates play a vital role in this process, ensuring that the parties involved are who they claim to be. When you use X.509 certificates, you establish trust between users and systems, protecting sensitive information from unauthorized access.
This verification process helps you avoid phishing attacks and data breaches, keeping your online interactions secure. In addition, strong identity verification can enhance your organization’s reputation and customer confidence.
By implementing robust authentication methods, you not only safeguard your data but also foster a secure environment for everyone involved.
Don't underestimate the value of these digital certificates in today's interconnected world.
Challenges in Managing X.509 Certificates
Managing X.509 certificates can be challenging, especially when you consider the complexities of issuance, renewal, and revocation. You might find it overwhelming to track multiple certificates across various systems, leading to potential security risks.
Managing X.509 certificates involves navigating complexities that can lead to security risks if not properly tracked and updated.
Additionally, the need to guarantee certificates are up-to-date can result in lapses that leave your organization vulnerable. Revocation can create additional complications, as you must verify all systems recognize the changes promptly.
There's also the challenge of maintaining compliance with various regulations, which can vary by industry. Moreover, if you’re dealing with a large number of certificates, the manual processes can be tedious and error-prone.
Streamlining these tasks is essential to avoid disruptions and enhance your overall security posture.
What Is Keytalk?
Keytalk is a powerful tool that simplifies X.509 certificate management.
With its core features, you'll find it easier to automate and secure your authentication processes.
Let’s explore how Keytalk can enhance your security strategy.
Keytalk Overview
 Control Semantic Ai Search For Your Business
Control Semantic Ai Search For Your BusinessIn today’s digital landscape, securing communications and identities is essential, and that's where Keytalk comes into play.
Keytalk is an innovative solution designed to simplify and strengthen X.509 authentication. By utilizing a unique approach to certificate management, it helps you efficiently issue, renew, and revoke digital certificates. This not only enhances security but also streamlines workflows within your organization.
With Keytalk, you gain visibility and control over your digital assets, allowing you to manage identities seamlessly. The platform integrates easily with existing systems, ensuring a smooth shift without disrupting your operations.
Ultimately, Keytalk empowers you to protect your communications and enhance trust in your digital interactions. It’s a smart choice for modern security needs.
Core Features Explained
Understanding the core features of Keytalk reveals how it addresses the complexities of X.509 authentication. Keytalk simplifies certificate management through automation, ensuring you can focus on your core tasks without getting bogged down by manual processes.
Its user-friendly interface allows you to easily generate, deploy, and revoke certificates, enhancing your security posture. Keytalk also offers seamless integration with existing systems, making it a versatile solution for various environments.
You’ll appreciate the real-time monitoring capabilities, which keep you informed about the status of your certificates and alert you to potential issues.
With advanced encryption and compliance features, Keytalk not only strengthens your authentication process but also helps you meet industry standards effortlessly. This makes Keytalk a smart choice for managing X.509 authentication.
How Keytalk Simplifies Certificate Management
Simplifying certificate management is essential for securing your organization’s communications, and that’s where Keytalk comes into play. With its intuitive platform, you can easily issue, renew, and revoke certificates without the usual hassle.
Keytalk automates many processes, reducing manual errors and saving you time. You’ll have a centralized view of all your certificates, making it simple to track their status and expiration dates.
Plus, with seamless integration into your existing systems, you won’t disrupt your workflow. Keytalk also provides clear notifications for upcoming renewals, ensuring you never miss a critical deadline.
Enhancing Security With Keytalk
While Keytalk streamlines certificate management, it also plays a significant role in enhancing your overall security posture. By automating the issuance and renewal of X.509 certificates, you reduce the risks associated with expired or mismanaged certificates.
Keytalk’s robust encryption protocols guarantee that your data remains secure during transmission, guarding against eavesdropping and man-in-the-middle attacks. You can also implement strong authentication measures, verifying the identity of users and devices accessing your network.
Keytalk ensures secure data transmission with strong encryption, protecting against eavesdropping and validating user identities.
With centralized visibility, you can quickly identify vulnerabilities and respond to potential threats. This proactive approach not only strengthens your defenses but also fosters trust among your users, guaranteeing that sensitive information stays protected.
Embrace Keytalk to elevate your security strategy effectively.
Streamlining Operations Through Automation
To streamline operations effectively, automating routine tasks can considerably reduce manual effort and minimize errors. By implementing automation tools, you can handle repetitive processes like certificate management and renewals seamlessly. This not only frees up your team’s time but also enhances productivity, allowing them to focus on higher-value activities.
With automation, you can guarantee consistency across your operations, reducing the risks associated with human error. For instance, automated alerts can notify you of impending certificate expirations, so you won’t have to worry about lapses in security.
In this way, you can maintain a robust authentication framework without the constant manual oversight. Embracing automation simplifies your workflow and strengthens your organization’s overall efficiency and security posture.
Real-World Applications of Keytalk
Keytalk offers a range of real-world applications that can greatly enhance your organization's security and efficiency. For instance, you can implement secure device authentication to guarantee that only trusted devices access your network. This helps prevent unauthorized access and protects sensitive data.
Additionally, Keytalk's automated certificate management streamlines the process of issuing and renewing X.509 certificates, reducing administrative overhead and minimizing the risk of human error.
You can also leverage Keytalk's integration capabilities with existing systems, making it easier to adopt strong authentication practices without overhauling your current infrastructure.
Getting Started With Keytalk for X.509 Authentication
When you're ready to enhance your organization's security through X.509 authentication, getting started with Keytalk is straightforward. First, sign up for an account on the Keytalk platform. You’ll need to configure your environment to integrate Keytalk's services seamlessly.
Follow the step-by-step onboarding guide provided by Keytalk to set up your certificate authority and define your authentication policies.
Once your setup is complete, you can start issuing X.509 certificates. Test the integration in a controlled environment to guarantee everything works as expected.
Don't hesitate to explore Keytalk's documentation for detailed insights and troubleshooting tips. With Keytalk, you’ll streamline your X.509 authentication process and bolster your organization’s security effectively.
Frequently Asked Questions
What Types of Organizations Benefit Most From X.509 Authentication?
Organizations that handle sensitive data, like financial institutions, healthcare providers, and government agencies, benefit most from X.509 authentication.
You’ll find that businesses requiring secure online transactions or remote access also thrive with this technology.
By using digital certificates to validate identities, you enhance security against unauthorized access.
If your organization values data integrity and confidentiality, implementing X.509 can markedly strengthen your security posture and build trust with your clients.
How Does Keytalk Integrate With Existing IT Systems?
How easily can your existing IT systems adapt to new security solutions?
Keytalk seamlessly integrates by utilizing APIs and connectors that link directly to your current infrastructure. It allows you to maintain your existing workflows while enhancing security.
You won’t have to overhaul your systems; instead, you’ll elevate your authentication processes. This integration guarantees you can implement robust security measures without disrupting your daily operations or requiring extensive retraining for your team.
Are There Specific Compliance Standards Keytalk Helps Meet?
Yes, there are specific compliance standards that Keytalk helps you meet.
It supports regulations like GDPR, HIPAA, and PCI-DSS by ensuring secure data handling and access control.
By using Keytalk’s solutions, you can streamline your compliance processes and maintain the required security measures for sensitive information.
This integration not only simplifies adherence to these standards but also enhances your overall security posture, making it easier for you to focus on your core business activities.
What Support Options Are Available for Keytalk Users?
When you’re maneuvering a complex system, wouldn’t it be reassuring to know help is just a click away?
Keytalk offers various support options to guarantee you get the assistance you need. You can access detailed documentation, user forums, and direct customer support through email or chat.
Plus, there are regular updates and training sessions to keep you informed. With these resources, you can confidently manage your authentication needs.
Can Keytalk Be Used for Non-Digital Certificate Applications?
Yes, Keytalk can be adapted for non-digital certificate applications.
You can utilize its underlying technology to enhance security measures for various systems beyond traditional certificates. By integrating Keytalk's capabilities, you can streamline processes, improve authentication methods, and maintain a high level of security.
Explore how to customize Keytalk's features to fit your specific needs, ensuring robust protection across different applications while optimizing efficiency and user experience.
Conclusion
In today's digital landscape, securing your systems with X.509 authentication is essential, and Keytalk makes that journey smoother than ever. By streamlining certificate management and enhancing security, you can focus on what truly matters—growing your business. Don’t let the complexities of certificate management bog you down; let Keytalk be your guiding light. Embrace this smart solution, and watch your security and operations flourish like a well-tended garden in the spring.